Complete Your Investigations Faster
Speed is critical to ensure you get the evidence before it is overwritten and you minimize the damage an attacker can do.
Cyber Triage maximizes the artifacts per second you process by:
- Identifying the artifacts that are relevant and showing them first.
- Recommending artifacts so that you quickly follow all leads.
- Integrating with SIEMs so that collections start ASAP.
Conduct More Comprehensive Investigations
Investigations need to be comprehensive to understand the full scope of the incident and remove the persistence mechanisms.
Cyber Triage gives you breadth by:
- Collecting dozens of artifact types based on numerous attack scenarios.
- Analyzing executables with 40+ malware scanning engines.
- Using threat intelligence to update collection methods and heuristics.
Flexible Deployments
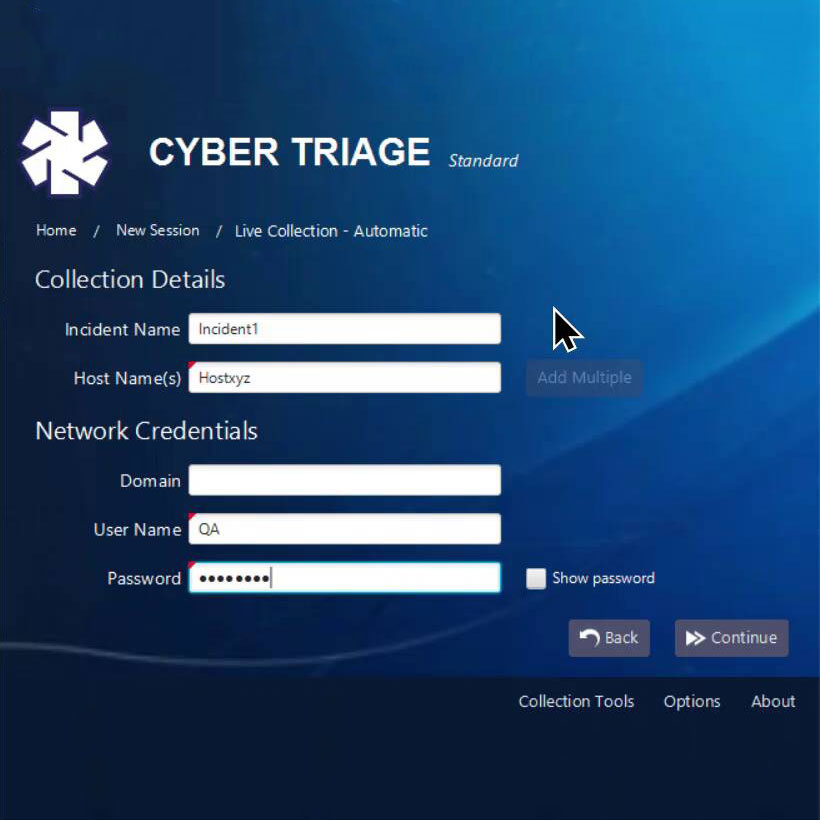
Investigations using Cyber Triage have four basic steps:
- Data is collected using an agentless collection tool that sends artifacts over the network, to USB, or S3.
- Artifacts are analyzed and scored using threat intelligence. Correlations are made between hosts.
- Responders review the artifacts and dive deeper based on what questions they need to answer.
- Additional hosts are collected from and added to the incident.
Cyber Triage has been designed to work in any scenario a Cyber First Responder finds themselves in. It can run on a laptop, the cloud, or an on-premise server.