| Product Type |
|---|
Elcomsoft Phone Breaker
Perform logical and over-the-air acquisition of iOS devices, break into encrypted backups, obtain and analyze backups, synchronized data and passwords from Apple iCloud.
- Break passwords and decrypt iOS backups with GPU acceleration
- Decrypt iCloud Keychain and Messages with media files and documents from iCloud
- Obtain synchronized data from Apple and Microsoft accounts
- Download iCloud backups and synced data with or without Apple ID password
Supports: local iOS backups (iTunes); iCloud and iCloud Drive backups; iCloud synced data (call logs, photos, browsing history etc.) Microsoft Account (with valid authentication credentials); iCloud authentication tokens.
Cloud Acquisition via Apple iCloud and Microsoft Account
Cloud acquisition is a highly effective way of retrieving up-to-date information backed up or synced by modern smartphones with their respective cloud services. Elcomsoft Phone Breaker supports the extraction of cloud backups and synced data from Apple iCloud and Microsoft Account, enabling remote acquisition of iPhone and iPad devices as well as Windows devices, Skype and other Microsoft software.
Online backups and synchronized data can be acquired by forensic specialists without having the original iOS device in hands. All that’s needed to access online data stored in the cloud service are the original user’s authentication credentials including the second authentication factor.
End-to-End Encryption in iCloud
Elcomsoft Phone Breaker enables access to iCloud data with end-to-end encryption. Protected categories include iCloud Keychain, iCloud Messages, Health, Screen Time and Maps data. Accessing end-to-end encrypted data requires the user’s full authentication credentials including second authentication factor, as well as a system password or screen lock password to one of the user’s devices.
iCloud Keychain
Elcomsoft Phone Breaker is the only tool on the market to access, extract and decrypt iCloud Keychain, Apple’s cloud-based system for storing and syncing passwords, credit card data and other highly sensitive information across devices. As opposed to authorizing a new Apple device, Elcomsoft Phone Breaker does not become part of the circle of trust and does not require a middleware device, thus offering truly forensic extraction of protected records.
Screen Time Passcode
The Screen Time passcode is an optional feature in iOS that can be used to secure the Content & Privacy Restrictions. Once the password is set, iOS will prompt for the Screen Time passcode if an expert attempts to reset the device backup password (iTunes backup password) in addition to the screen lock passcode. As a result, experts will require two passcodes in order to reset the backup password: the device screen lock passcode and the Screen Time passcode. Since the 4-digit Screen Time passcode is separate to the device lock passcode (the one that is used when locking and unlocking the device), it becomes an extra security layer effectively blocking logical acquisition attempts.
By extracting and analyzing Screen Time information, experts can extract Screen Time passwords,
thus gaining the ability to remove Screen Time protection and/or to reset the password protecting local (iTunes) backups. This in turn makes logical acquisition easily possible.
iCloud Messages and Health Data
Apple supports Health and Messages sync through iCloud. Elcomsoft Phone Breaker is the first tool on the market to extract and decrypt messages from iCloud complete with attachments, extract and decrypt Health data. To access Health and Messages, the login and password to the user’s Apple Account, one-time code to pass Two-Factor Authentication and a screen lock password or system password for one of the already enrolled devices are required.
Extract Skype Conversations, OneDrive and Vault Files
The tool allows downloading of Skype conversation histories, files, contact lists and metadata directly from the user’s Microsoft account. Individual and group chats, text messages and attachments are extracted. The downloading of the entire conversation of an average Skype history only takes minutes!
For deleted chats and messages as well as for files purged from Skype servers after the 30-day retention period, Elcomsoft Phone Breaker can obtain metadata such as the date and time the file was deleted, the file’s name and size, sender’s Skype ID and the name of the chat.
The tool can download files from the user’s OneDrive. The downloaded files include the content of OneDrive Vault, which is a protected cloud storage for keeping the most sensitive kinds of information. In addition, the tool can obtain metadata for files that have been recently deleted from OneDrive.
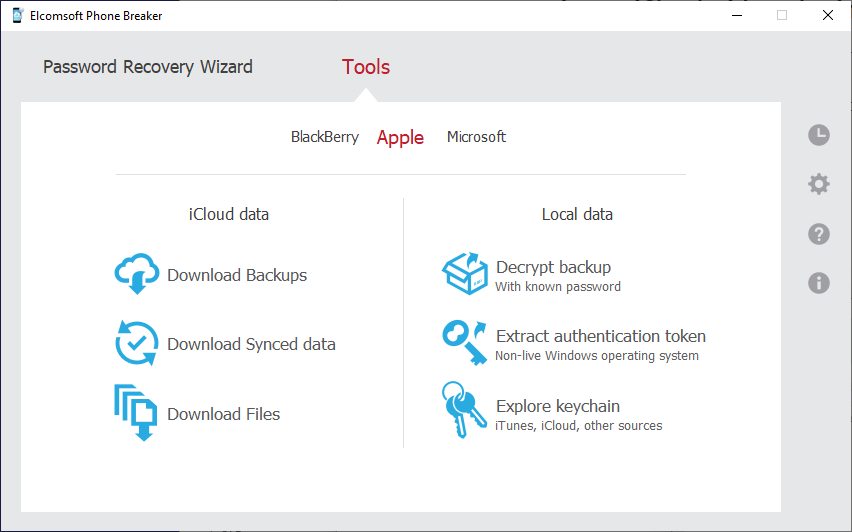
Elcomsoft Phone Breaker: main window
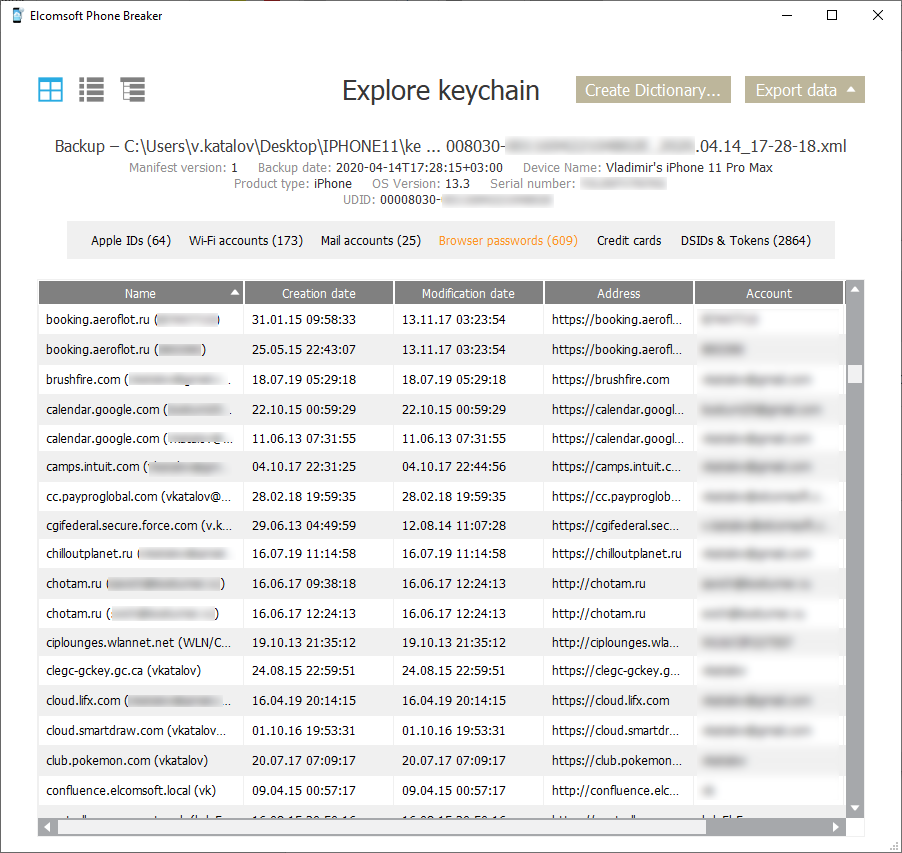
Elcomsoft Phone Breaker: explore keychain
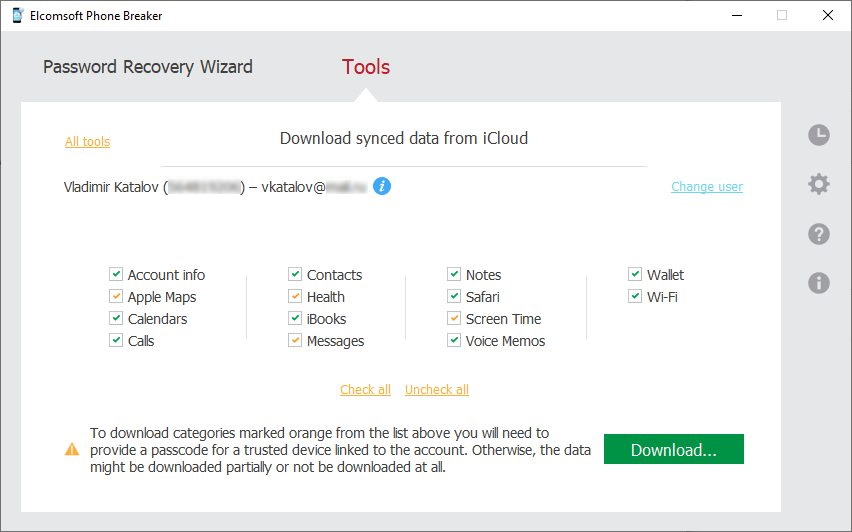
Elcomsoft Phone Breaker: download synced data from iCloud
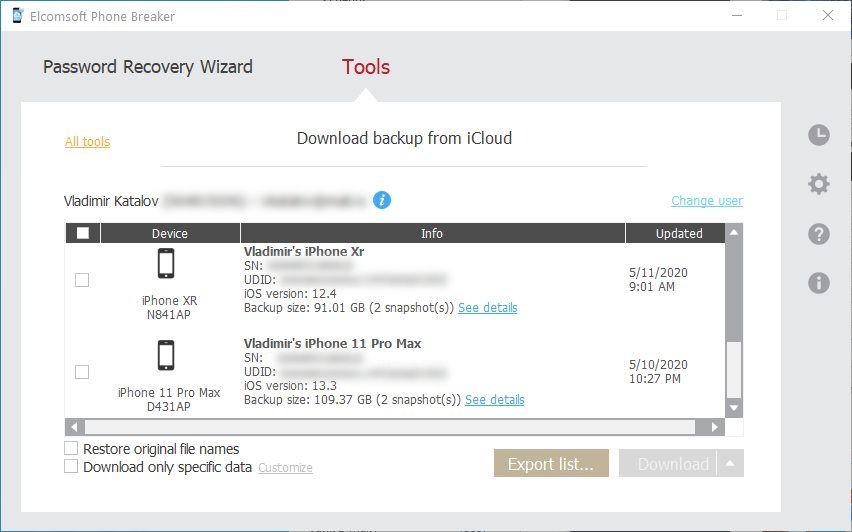
Elcomsoft Phone Breaker: download backups from iCloud
All Features and Benefits
Download iCloud Backups with Selective Access
iCloud backups are enabled by default, and are created automatically on a daily basis when users charge their devices while connected to a Wi-Fi network. Cloud backups contain a large amount of evidence including third-party app data. Unlike local (iTunes) backups, cloud backups cannot be encrypted with a password. Apple does not provide a way to download iCloud backups other than restoring to a new device. Cloud backups can only be downloaded from the user’s Apple account with a third-party tool such as Elcomsoft Phone Breaker.
Downloading a large backup for the very first time can potentially take hours. Subsequent updates are incremental, and occur much faster. If speed is essential, Elcomsoft Phone Breaker offers the ability to quickly acquire select information and skip data that’s taking the longest to download (such as music and videos). Information such as messages, attachments, phone settings, call logs, address books, notes, calendars, email account settings, camera roll, and many other pieces of information can be pre-selected and downloaded in just minutes, providing investigators with near real-time access to essential information.
Recover Password-Protected Apple iTunes Backups
Elcomsoft Phone Breaker enables forensic access to password-protected backups for smartphones and portable devices based on the Apple iOS platform. The password recovery tool supports all Apple devices running all versions of iOS including the iPhone, iPad and iPod Touch devices of all generations released to date.
Retrieve Cloud Data: Apple iCloud and Microsoft Account
Cloud acquisition is a great way of retrieving information stored in mobile backups produced by Apple iOS, and a handy alternative when exploring Windows Phone, Windows 10 Mobile and desktop Windows 10 devices. Elcomsoft Phone Breaker can retrieve information from Apple iCloud and Microsoft Account provided that original user credentials for that account are known.
Online backups can be acquired by forensic specialists without having the original iOS or Windows device in hands. All that’s needed to access online backups stored in the cloud service are the original user’s credentials including Apple ID or Microsoft Account accompanied with the corresponding password. Accounts with two-factor authentication are fully supported.
Access iCloud without Login and Password
If the user’s Apple ID and password are not available, Elcomsoft Phone Breaker may be able to use an alternative authentication method.
First, one can use a binary authentication token to access a limited set of iCloud data. The use of authentication tokens allows bypassing two-factor authentication even if no access to the secondary authentication factor is available. Authentication tokens can be extracted from Windows and macOS computers, hard drives or forensic disk images with a built-in tool.
The second method offers unrestricted access to everything stored in the user’s iCloud account including end-to-end encrypted data. Instead of using the login and password, you can authenticate to iCloud with the user’s trusted iOS device. By using a trusted device, experts benefit from unrestricted access to all kinds of information stored in the user’s iCloud account including the iPhone backups and end-to-end encrypted data. The trusted device must be unlocked and compatible with a jailbreak or the included agent app.
Extract Synced Data
iPhones automatically sync certain types of data with iCloud in real time. Elcomsoft Phone Breaker automatically downloads synced data including call logs, contacts, notes (included deleted notes and attachments), calendars as well as Web browsing activities including Safari history (including deleted records), bookmarks and open tabs. Unlike iCloud backups that may or may not be created on daily basis, synced information is pushed to Apple servers just minutes after the corresponding activity has taken place. Once uploaded, synced data can be retained for months with no option for the end user to clear the data or disable the syncing.
Elcomsoft Phone Breaker supports the following types of synced data:
- Messages in iCloud: complete with media and file attachments
- Health data (iOS 11+)
- iCloud Keychain
- Screen Time passwords (iOS 12+)
- Safari (browsing history, bookmarks, tabs opened on user’s devices)
- Calendars, notes, contacts and Voice Memos
- Call logs (information about calls made and received) (iOS 12 and older)
- Apple Maps (routes, places, searches)
- Wi-Fi (wireless access points, MAC addresses, date and device added)
- Wallet (everything except payment data)
- Account info (comprehensive information about the user and devices registered on the Apple ID account)
- iBooks (documents including PDF files that were added by the user)
In addition, Elcomsoft Phone Breaker can extract FileVault 2 recovery keys from the user’s iCloud account, and use these keys to decrypt encrypted HFS+ disk images without a password.
iCloud Files
In addition to iCloud backups, Elcomsoft Phone Breaker can download files stored in the user’s iCloud account such as documents or spreadsheets, third-party application data (such as WhatsApp own backups, Passbook/Wallet data etc.), and more. Files from a synced Mac such as Desktop, Documents, and Trash can be extracted. Some of this data (mostly documents) is available using the iCloud feature on Windows and macOS systems, but most files are only accessible using Elcomsoft Phone Breaker. The exact set of data available may depend on the version of iOS installed, iCloud synchronization settings, the list of applications installed on the devices connected to the given account, and the options set in these applications. Note that there is no email notification sent by Apple when downloading files from iCloud.
Note: this functionality is only available in Forensic edition
Access Photos in iCloud Photo Library
Apple’s iCloud Photo Library is designed to help users store and synchronize media files between multiple devices. If iCloud Photo Library is enabled, media files are no longer saved to iOS iCloud backups. As a result, acquiring iCloud backups or downloading files stored in iCloud Drive does not automatically provide access to media files stored in the iCloud Photo Library.
Elcomsoft Phone Breaker can extract photos and videos stored in the user’s iCloud Photo Library. In addition to existing files, Elcomsoft Phone Breaker can extract media files that have been deleted from the Library during the past 30 days. Selective downloads are possible by specifying which user-created albums to download.
Device-based iCloud Authentication
Use a trusted iPhone or iPad to perform iCloud extraction without the need to input a password or solve the two-factor authentication challenge. This new authentication method makes every type of data extractable including cloud backups, iCloud photos, and synchronized data including the end-to-end encrypted types.
GPU Acceleration and Advanced Attacks
ElcomSoft offers a highly efficient, cost-effective solution to lengthy attacks by dramatically increasing the speed of password recovery when one or more supported video cards are present. GPU acceleration reduces the time required to recover iPhone/iPad/iPod and BlackBerry backup passwords by orders of magnitude. The latest generation of ElcomSoft GPU acceleration technology supports unlimited numbers of AMD or NVIDIA boards.
Multiple diverse GPU acceleration units can be used at the same time, allowing mixing multiple generations of compatible video cards to extend existing systems by adding new acceleration hardware instead of replacing.
Advanced dictionary attack with customizable mutations target the human factor and password reuse. The tool supports a variety of mutations, trying hundreds of variants for each dictionary word to ensure the best possible chance to recover the password.
Note: not applicable to MacOS X edition
Extract, Decrypt and View Passwords Stored in iOS Keychain
iOS offers a highly secure, encrypted storage for many types of data. Stored Web forms and browser passwords, email accounts, application passwords and authentication tokens (including Apple ID account token) are stored securely in keychains that are encrypted with hardware keys unique to each individual device.
Elcomsoft Phone Breaker can extract and decrypt iOS keychain from local (iTunes-style) password-protected backups. The built-in Keychain Explorer tool allows browsing and exploring keychain items on the spot. Note: the keychain can be only decrypted when extracted from local password-protected backups.