SOC Class- Four Day Training
– By Christopher Crowley
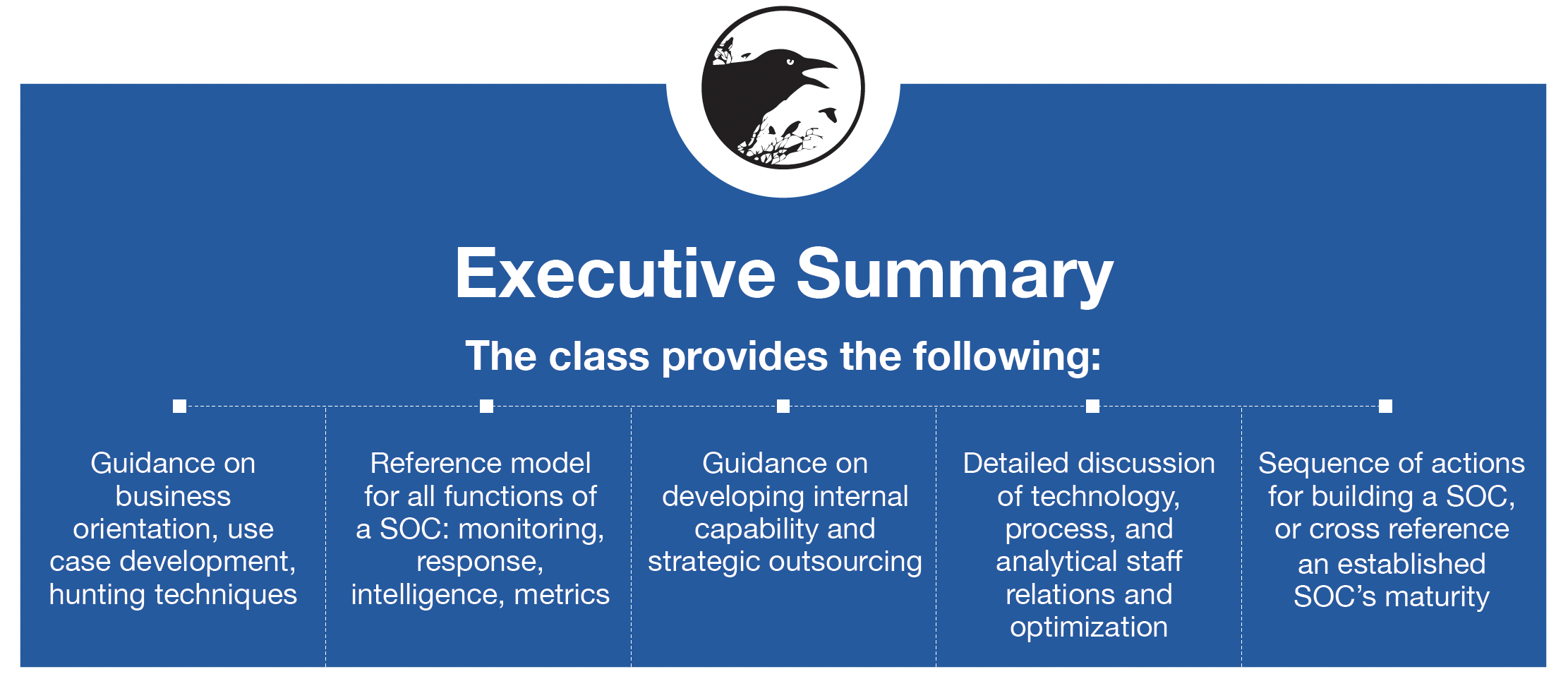
This course provides a comprehensive picture of a Cyber Security Operations Center (CSOC or SOC). Discussion on the technology needed to run a SOC are handled in a vendor agnostic way. In addition, technology is addressed in a way that attempts to address both minimal budgets as well as budgets with global scope. Staff roles needed are enumerated. Informing and training staff through internal training and information sharing is addressed. The interaction between functional areas and data exchanged is detailed. Processes to coordinate the technology, the SOC staff, and the business are enumerated. After attending this class, the participant will have a roadmap (and Gantt chart) for what needs to be done in the organization seeking to implement security operations. Ideally, attendees will be SOC managers, team leads in security specializations or lead technical staff, security architects. CIO, CISO or CSO (Chief Security Officer) is the highest level in the organization appropriate to attend.
What is needed to proceed?
A trustworthy, external, objective party familiar with varying deployments of security operations, global compliance issues, and the technical needs of running a SOC is needed. Your organization’s willingness to review its current security operations practices, and deploy both strategic and tactical adjustments to its current course is needed.
SECURITY OPERATIONS CENTRE Maturity Assessment
-
I have a SOC already, why would I need a SOC Maturity Assessment?
Threats to your environment don’t respect compliance standards.
Threats to your environment study, plan, and execute their efforts according to the most likely path to their success. Your business reacts to market factors, customer demand, supply chain, and opportunities. To do so, strategy is reviewed and adjusted. Likewise, a SOC maturity assessment assures your defensive resources are most effectively defending against current threat techniques.
- Security Operations Maturity Assessment
- Documentation Collection
- Framework crosswalk
-
Flexible, based in business specific needs, using proven, objective, industry standard methodology, performed by an industry expert
-
Document review only
Technical assessment, red-teaming, adversary simulation available on a customized basis.
-
Assessment schedule is three months in duration
Depends on organization’s ability to collect and provide requested materials.
-
Delivered Guidance
Adjusted metrics, SOC operations modifications plan: use cases, threat hunting, operational changes, staff recommendations, self-improvement program.