Web API is extremely handy as it allows you to use it in scripts, via CLI tools like curl, and simply by typing commands in the browser address bar.
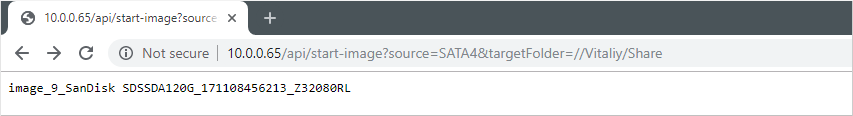
1. Start imaging a source drive plugged into TaskForce SATA 4 port.
2. Track imaging session status using task key received in response to the command above.
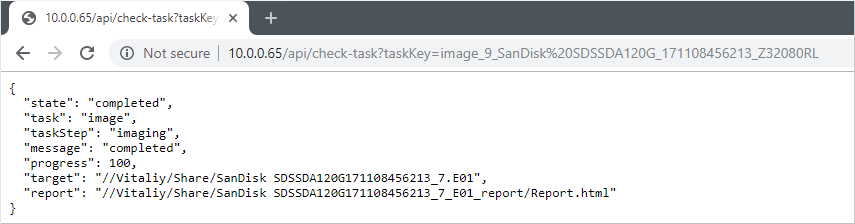
Here is what it looks like in action:
Instantly start imaging all source drives
Imagine you have 12 TaskForce ports switched to Source mode and source drives plugged into them. Firmware version 2019.7 enables you to instantly launch 12 imaging sessions with the power of Web API.
Python script utilizes /start-image API request and prints task keys of all started imaging sessions.
Automatic forensic analysis upon imaging completion
With TaskForce, you can track the status of the started imaging sessions using /check-task API request. It reports the imaging progress enabling you (or your code) to notice when the task gets completed. Once this notification is received, it makes perfect sense to automatically start the forensic analysis of the target image. Powershell script below shows how one can create this kind of automation flow:
- Start imaging a source drive on TaskForce SATA port 4 to the target folder \\Vitaliy\Share
- Wait for imaging completion using /check-task
- Launch Autopsy Ingest via command-line when the target image is ready
All changes
New Features
Introduction of simple Web API with 5 commands:
- /start-image – launches an imaging session
- /check-task – returns the status of an imaging task
- /scan-devices – find all source drives available for imaging
- /stop-task – stops imaging session
- /help – opens API documentation
New system setting:
- Store shared folder logins and passwords in TaskForce
Case ID is now displayed in the device selection window.
Bugfixes
- Target drive serial numbers were missing in imaging reports
- Restoring file image from password-protected network folder denied
- File selection window was too wide when open on mobile phone
- WrappedApiResultException when parsing partition with bad sectors



