Oxygen Forensic® Detective v.14.6 is now available!
New features include:
- Bruteforce for MTK Android extractions – OnlyFans cloud extraction.
- User Searches section.
- Import of WonderShare backups.
For a full list of updates, refer to the “What’s New” file in the Oxygen Forensic® Detective “Options” menu.
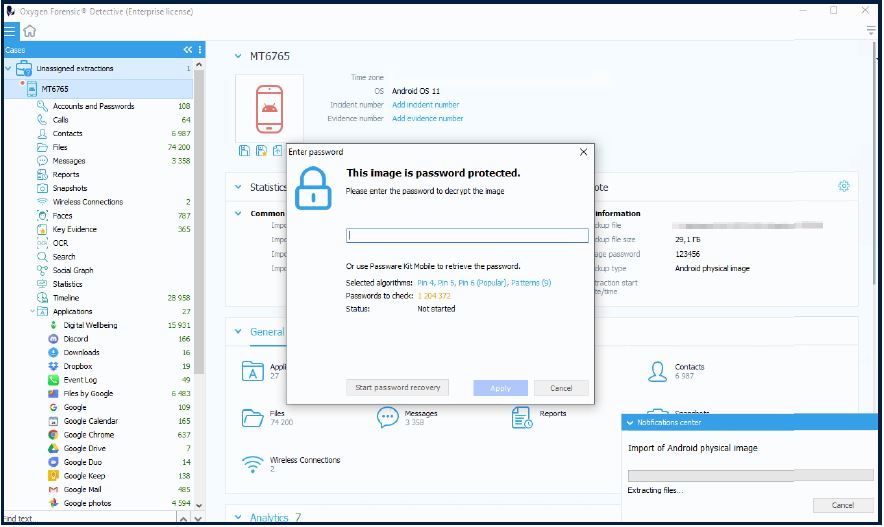
Bruteforce for MTK extractions
You can now bruteforce passcodes to decrypt extractions of MTK-based Android devices that have FBE (File-Based Encryption). Once you start importing an extraction into Oxygen Forensic® Detective, you will see a window where you can either enter a passcode or enable brute force with the built-in Passware Kit Mobile module. You can also create custom attacks. Supported devices include: Oppo, Realme, and Xiaomi models based on the MT6765 chipset: Xiaomi Poco C31, Xiaomi Redmi 9 Activ, Xiaomi Poco C3, Xiaomi Redmi 9, Oppo A15, Oppo A15s, Realme C21, Realme C20, Realme C12, etc.
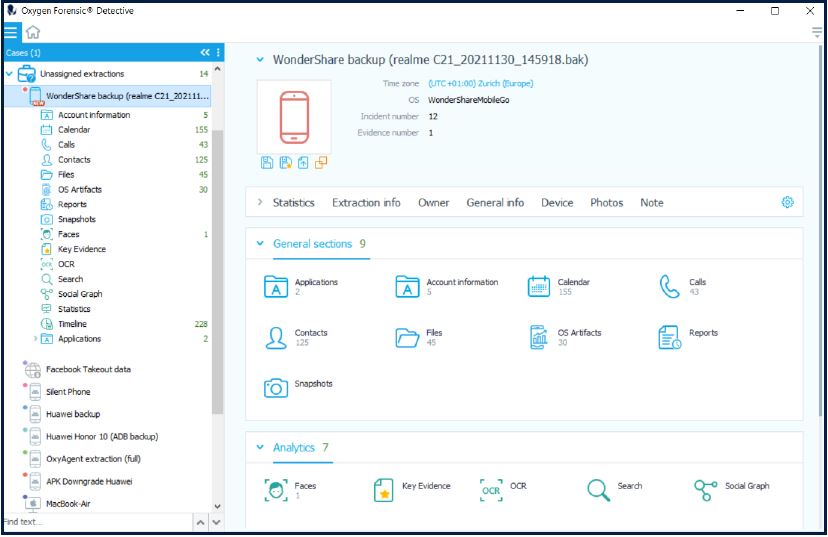
Import of WonderShare backups
Oxygen Forensic® Detective v.14.6 introduces support for WonderShare MobileGo and Mobile Trans backups made from Apple iOS and Android devices.
To import this backup type into our software, click the WonderShare backup option under the Third-party extractions menu on the software Home screen and follow the instructions. Parsed evidence sets will include contacts, calls, calendars, accounts, and other available data.
Import of Facebook account data
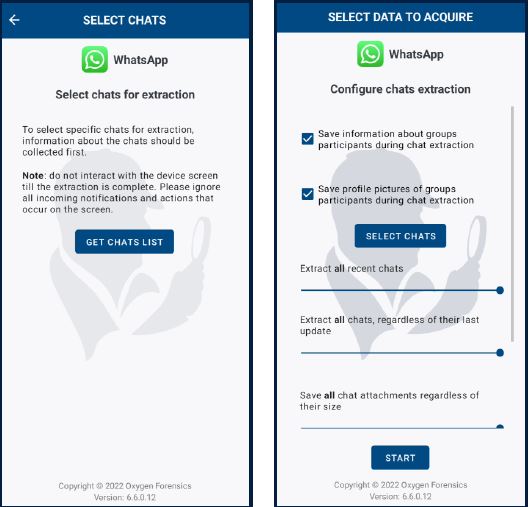
Support for WhatsApp QR Multi-Device
Version 14.6 expands the capability of importing and analyzing Facebook account copy saved in HTML format by enabling the import of Facebook account data in JSON format.
Mobile Forensics
We’ve added the ability to extract the full file system and keychain data via checkm8 vulnerability from Apple iOS devices running iOS 15.6 Beta. If running iOS 16.0 Beta, full file system and keychain data can be extracted from iPhone 8, iPhone 8 Plus, and iPhone X. The extraction algorithm is the same as for iOS 15 devices.
iOS Agent updates
In Oxygen Forensic® Detective v.14.6 we extend our support of iOS Agent to the devices with iOS versions 15.0 – 15.1.1. The list of supported devices includes: iPhone 8, iPhone 8 Plus, iPhone X, iPhone XS, iPhone XS Max, iPhone XR, iPhone 11, iPhone 11 Pro, iPhone 11 Pro Max, iPhone SE (2nd gen), iPhone 12, iPhone 12 Mini, iPhone 12 Pro, iPhone 12 Pro Max, iPhone 13, iPhone 13 Mini, iPhone 13 Pro, and iPhone 13 Pro Max.
Device Extractor updates
In this release we’ve focused on extraction method updates. We’ve redesigned three methods and incorporated them in the new Device Extractor.
-
Logical extraction via Android Agent using Wi-Fi
-
Physical extraction of memory cards
-
Extraction of DJI dronesThe Tools menu and Notifications panel were added to the Oxygen Forensic® Device Extractor interface. From the Tools menu, you can launch our old Oxygen Forensic® Extractor if necessary.
The Tools menu and Notifications panel were added to the Oxygen Forensic® Device Extractor interface.
From the Tools menu, you can launch our old Oxygen Forensic® Extractor if necessary.
App support
Oxygen Forensic® Detective v.14.6 supports the following new apps:
-
Skout,
-
TigerConnect,
-
Omlet Arcade
-
Google Meet
-
KiteTech Notepad Notes
The total number of supported app versions exceeds 33,000.
Cloud Forensics
OnlyFans data extraction
Using the latest Cloud Extractor, you can acquire data from OnlyFans cloud accounts. Authorization is available via login credentials, tokens, as well as with the corresponding Google or Twitter account. If a 2FA is enabled, there is an opportunity to receive a code via SMS, call, or use a backup code. Extracted evidence will include account information, payment methods, chats, contacts, comments, sessions, and other available data.
Other Cloud Extractor updates
We’ve completely redesigned data extraction for the Telegram cloud. Now more data types will be extracted.
We’ve also added the ability to view the information about available WhatsApp Google backups. This information will include phone number, backup size, backup creation date, and the WhatsApp app version with which this backup was created.
We’ve updated support for Samsung Health and AirBnB.
Computer Artifacts
KeyScout updates
With the updated Oxygen Forensic® KeyScout you can collect the following new computer artifacts on Windows computers:
-
UserAssist
-
Most recently used (MRU)
-
setupapi.dev.log
-
RDP Cache
-
Event Log (updated support)
-
Jump lists and LNK files (updated support)
General
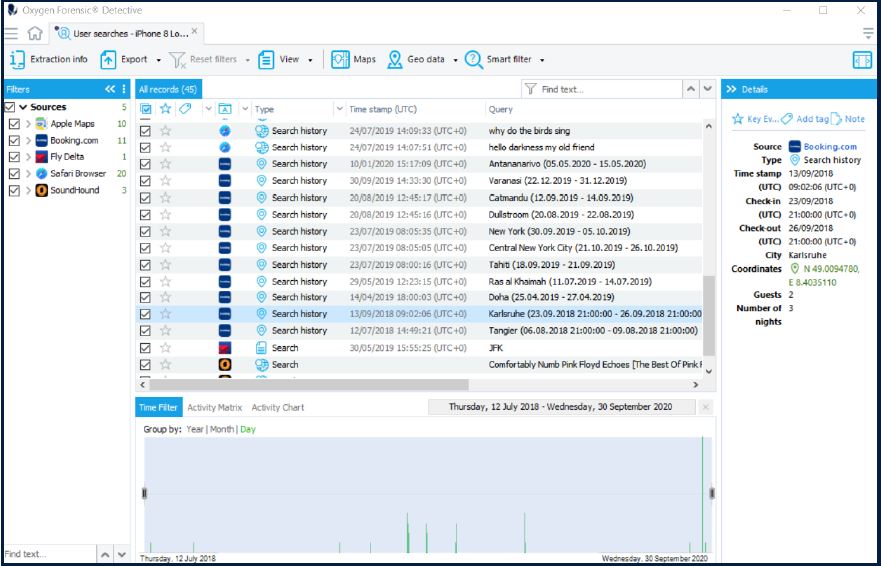
User Searches section
The User Searches is a new section that is now available under the General sections in Oxygen Forensic® Detective.
This section automatically collects all the user searches from extracted apps (Web Browsers, Social Networks, Travel apps, etc.) and shows them in a single list. Now analysis of user searches is much easier.
Advanced filters in the Files section
We’ve added the ability to configure custom filters in the Files section using the Advanced filters button on the toolbar.
Now you can create your own filter using various criteria: status, name, specified time period, size, hash sets, etc.
Resolved Issues
- No images were extracted via Oxy Agent when the File Structure was selected.
- “Can`t InitializeIAViSEngine” error on Image Categorization.
- “Folder Name” field parsed as “File Name” from Windows USN Journal.
- Error when trying to find similar faces in the “faces sets” section.



